Exploiting Apache Tomcat & Abusing LXD Membership for PrivEsc

 Tabby is a linux box rate as easy. We need to get /etc/tomcat9/tomcat-users.xml file to collect credential through LFI. Then, we could upload WAR file to victim to gain initial shell. To move into ash shell, we have to crack the backup zip file. To escalate into root, we could abusing lxd group membership to obtain root privilege.
Tabby is a linux box rate as easy. We need to get /etc/tomcat9/tomcat-users.xml file to collect credential through LFI. Then, we could upload WAR file to victim to gain initial shell. To move into ash shell, we have to crack the backup zip file. To escalate into root, we could abusing lxd group membership to obtain root privilege.
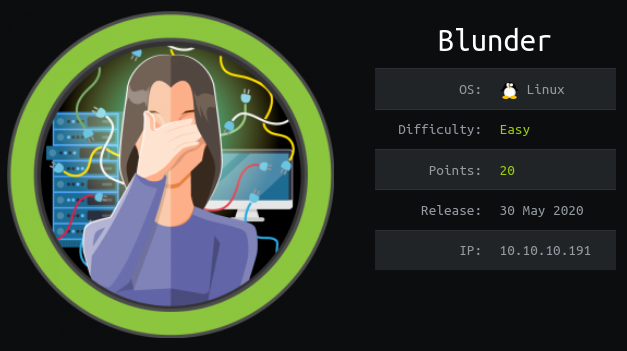 Blunder is a linux box rate as easy. We need to obtain credential of Bludit v3.9.2 by bruteforce login in order to get a shell. Then, enumerate Bludit files to get user password to switch user into hugo. From there, we could abuse sudo vulnerability to gain root shell.
Blunder is a linux box rate as easy. We need to obtain credential of Bludit v3.9.2 by bruteforce login in order to get a shell. Then, enumerate Bludit files to get user password to switch user into hugo. From there, we could abuse sudo vulnerability to gain root shell.
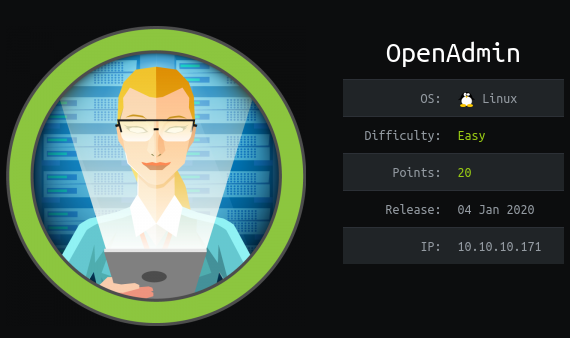 It has an OpenNetAdmin Web-based framework vulnerable to execution of Remote Code. We will compromise all users on the box after collecting some passwords and recon. One account has a sudo entry with nano root permissions which allows root privileges to raise.
It has an OpenNetAdmin Web-based framework vulnerable to execution of Remote Code. We will compromise all users on the box after collecting some passwords and recon. One account has a sudo entry with nano root permissions which allows root privileges to raise.
 In order to gain root shell, we need to escalate our privilege from local user to root to have best permission on the current system. Privilege escalation could be exploit by different techniques depending on how the linux system is configured by system admin. Here, we can learn different techniques to obtain root shell.
In order to gain root shell, we need to escalate our privilege from local user to root to have best permission on the current system. Privilege escalation could be exploit by different techniques depending on how the linux system is configured by system admin. Here, we can learn different techniques to obtain root shell.